Okay, so he mailed the authenticator verifier and amongst other info was the summary and the results:
SPF check: neutral
“iprev” check: pass
DKIM check: none
SpamAssassin check: ham
Spam Assassin Check Details
Result: ham (1.0 points, 5.0 required)
0.8 BAYES_50 BODY: Bayes spam probability is 40 to 60%
DKIM Results
none: The message was not signed.
pass: The message was signed, the signature or signatures were
acceptable to the ADMD, and the signature(s) passed verification
tests.
fail: The message was signed and the signature or signatures were
acceptable to the ADMD, but they failed the verification test(s).
policy: The message was signed, but some aspect of the signature or
signatures was not acceptable to the ADMD.
neutral: The message was signed, but the signature or signatures
contained syntax errors or were not otherwise able to be
processed. This result is also used for other failures not
covered elsewhere in this list.
temperror: The message could not be verified due to some error that
is likely transient in nature, such as a temporary inability to
retrieve a public key. A later attempt may produce a final
result.
permerror: The message could not be verified due to some error that
is unrecoverable, such as a required header field being absent. A
later attempt is unlikely to produce a final result.
SPF Results
none: Either (a) no syntactically valid DNS domain name was extracted from
the SMTP session that could be used as the one to be authorized, or
(b) no SPF records were retrieved from the DNS.
neutral: The ADMD has explicitly stated that it is not asserting whether
the IP address is authorized.
pass: An explicit statement that the client is authorized to inject mail
with the given identity.
fail: An explicit statement that the client is not authorized to use the
domain in the given identity.
softfail: A weak statement by the publishing ADMD that the host is probably
not authorized. It has not published a stronger, more definitive policy
that results in a “fail”.
temperror: The SPF verifier encountered a transient (generally DNS) error
while performing the check. A later retry may succeed without further
DNS operator action.
permerror: The domain’s published records could not be correctly interpreted.
This signals an error condition that definitely requires DNS operator
intervention to be resolved.
“iprev” Results
pass: The DNS evaluation succeeded, i.e., the “reverse” and
“forward” lookup results were returned and were in agreement.
fail: The DNS evaluation failed. In particular, the “reverse” and
“forward” lookups each produced results, but they were not in
agreement, or the “forward” query completed but produced no
result, e.g., a DNS RCODE of 3, commonly known as NXDOMAIN, or an
RCODE of 0 (NOERROR) in a reply containing no answers, was
returned.
temperror: The DNS evaluation could not be completed due to some
error that is likely transient in nature, such as a temporary DNS
error, e.g., a DNS RCODE of 2, commonly known as SERVFAIL, or
other error condition resulted. A later attempt may produce a
final result.
permerror: The DNS evaluation could not be completed because no PTR
data are published for the connecting IP address, e.g., a DNS
RCODE of 3, commonly known as NXDOMAIN, or an RCODE of 0 (NOERROR)
in a reply containing no answers, was returned. This prevented
completion of the evaluation. A later attempt is unlikely to
produce a final result.
So with that high ham score I assume cburn11 was right about all my dad’s mail being seen as spam and being put on hold.
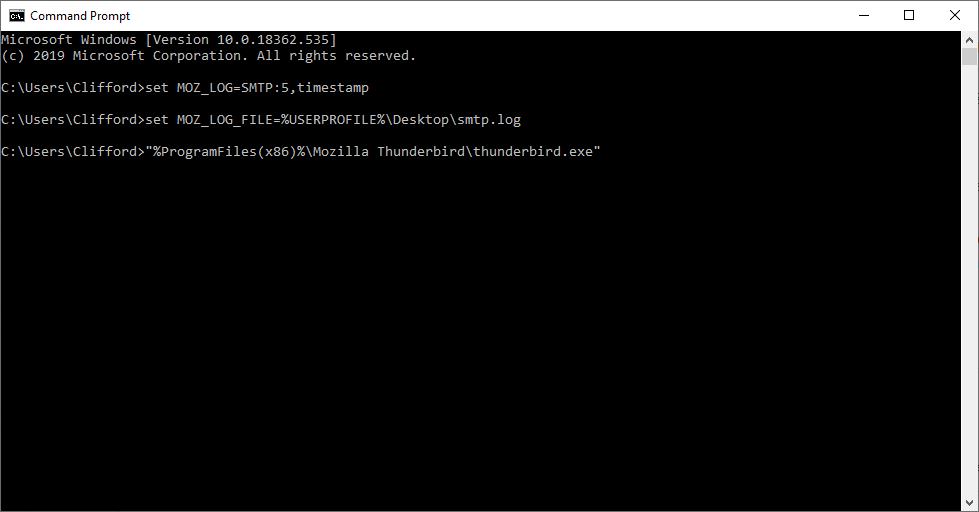
 My dad and I can’t get the log file to work now. The file keeps coming up blank. I can’t see what I’m missing / doing wrong.
My dad and I can’t get the log file to work now. The file keeps coming up blank. I can’t see what I’m missing / doing wrong.