Edit: SOLVED! Just needed to check “Don’t Pull Routes” in the openVPN settings, and set the gateway in the LAN interface firewall rules to the PIA’s gateway. Initially this caused some DNS leaking problems but that was resolvable by portforwarding the DNS port from the LAN net (source) to the VPN (destination). Unrelated thing learned: don’t use public routable IP addresses for internal networks.
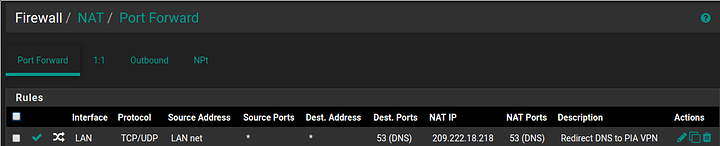
Port Forward Rule to prevent DNS leaking
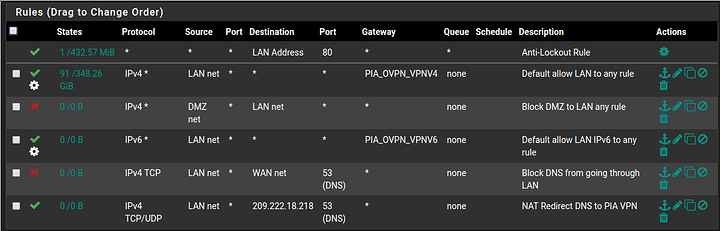
Working LAN interface Firewall Rules
Original Post:
Hi, first time poster here!
I set up my LAN to use PIA via openVPN according the the Whole Network VPN video on the Level1Linux channel. Everything on the LAN works fantastic and all my traffic has been tunneled through the VPN. However, the DMZ no longer has access to the internet, although the DNS lookup still appears to be working. Anything I may be doing wrong?
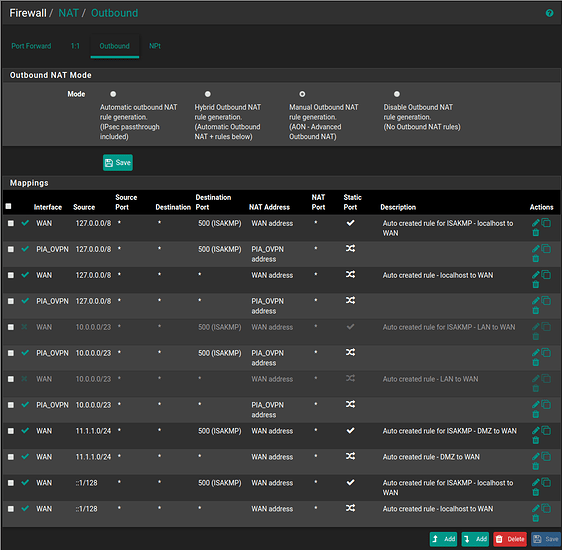
Here are my NAT outbound rules
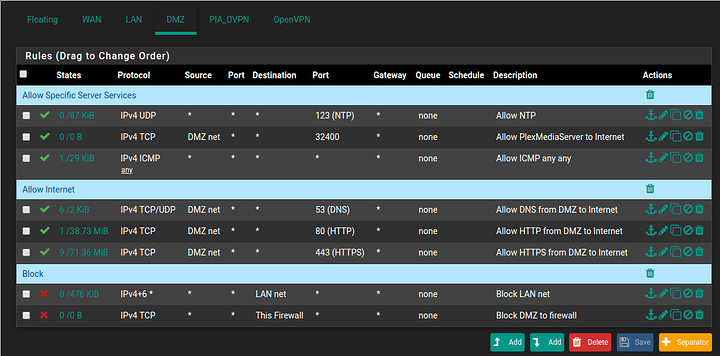
Here are the firewall rules on the DMZ interface
If there are any additional information that I left out, let me know. Thank you for your help!
-Carpathian