Yes, the 2gb server would be fine.
Wireguard is pretty light on ram and storage requirements, same with pihole.
https://docs.pi-hole.net/main/prerequisites/
Yes, the 2gb server would be fine.
Wireguard is pretty light on ram and storage requirements, same with pihole.
https://docs.pi-hole.net/main/prerequisites/
Not a criticism, but I really chuckled to myself:
If you’re reading this because you’re following an online tutorial on
installing WireGuard, please contact the authors to request that they
simplify their instructions to simply:$ sudo apt install wireguardThis PPA is no longer required for WireGuard. Press CTRL+C, and do not
proceed with adding it.
I get that the project planning, script, tests, recorded voice over, and the b-roll are done at different times, and parts would have been completed months ago, but might be worth mentioning to the authors of the guide @ryan and co followed, so they can update their guide.
the PPA says it only has packages for 14.04, and anyone running that, should probably update their distro anyway, if they are in a position to need WireGuard .
As a genuine question, the 2gb linode for $10/mo lists network traffic at about 1 TB/mo.
I presume this would be share between inbound and outbound? And as the VPS is running as a pass through, it would run out of data at 500GB each way? still a lot of hi-res YouTube/whatever/
what are the overages like on a linode? and would most of the tiers have the same cap (1TB/mo) so like a heavy user data hungry user might spin up additional nodes for more bandwidth?
[edit] by which I mean to say, 1TB is loads, but does it count inbound And outbound traffic, or just inbound Or outbound?
There’s also Algo by Trail of Bits. Spin up a Ubuntu machine and set a couple of config options then it automatically sets up sane defaults and the apt equivalent of yum-cron for you.
I switched over from OpenVPN to an Algo Wireguard server about 8 months ago, zero issues thus far 
Thank you @ryan for the tutorial.
I was only a little bit confused that I had to forward the Wireguard port on my home router. Does this mean that this setup won’t work when I go and sit with my laptop in a Starbucks?
A follow up on how to get this working with IPv6 as well would be very welcome.
I don’t know if it is just me but the official WireGuard website seems very thin on end user documentation.
EDIT:
I think I have this working via IPv6 now. At least it tests ok from https://ipv6-test.com
Not 100% sure which step got it working. If I am feeling energetic I will tear it down / rebuild it and post my steps.
Do you use ip6 from home to vps, then out to ip4 for “the Internet” or does it stay ip6 the other end?
I spent a lot of time banging my head against the wall to get this to work. To anyone else who gets stuck with handshake connect, try
ufw allow in on wg0 to any
to allow wireguard through your firewall.
Hiya folks. I’m sorry if this is a dumb question.
I’m seriosly considering this, but I want to be sure I understand.
Say I set up this virtual server which is running in a data center somewhere.
All my traffic is encrypted between me and that virtual server, but to the outside world it looks like all my traffic is coming from that virtual server’s IP address, right?
So the outside world can trace my traffic back to this particular virtual server in this particular data center, right?
And whoever runs this data center knows that my own IP address (the one I’m tring to keep private), is associated with this virtual server, right?
Am I still relying on a 3rd party to keep my IP address private?
I don’t understand how this method is neccesarily more secure than any other VPN.
I’m sure I’m missing something important here. Can anybody explain it to me like I’m dumb?
You have it about right.
It just isolates the traffic from your ISP, and potentially your government*
The real benefit might be for mobile devices, which might connect through untrusty and unsecure connections.
*your government will be able to get your details from the hosting site, but it might reduce the casual immoral inspection of people’s private traffic, because of the extra hoop.
Is this done on server or client side?
server side?
i figured. But I honestly am a windows user. This is bugging me. But I did manage to the minecraft sql working when dynamic couldn’t xD
Yeah Boi!
Admin_Evil_God next…
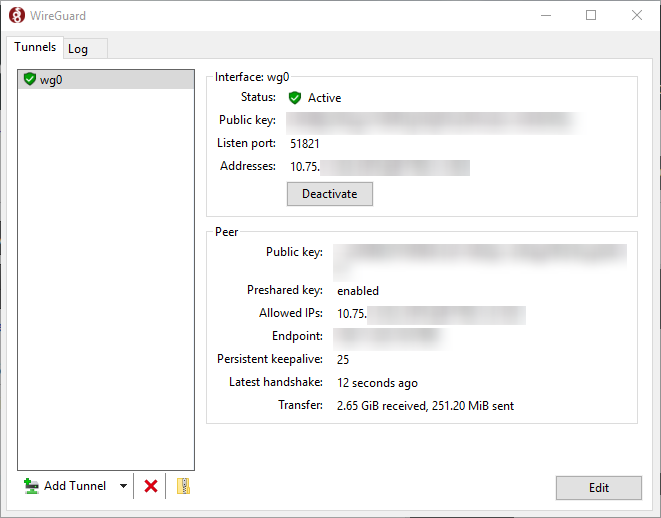
I have a Wireguard Site-to-Site from my home & linode for self hosting and a wireguard tunnel windows-to-windows so I can RDP into my work machine quickly.
It’s nice that they have a setup tool like that. I hope they make one for Linux or distros start to include it in their guis
Android has a nice client set up utility as well. I kind of want to add a pier and have that available but honestly I don’t need it since I can already publicly access most of my stuff through the site to site tunnel I already have
sudo wg showYes I know we all know about the terminal and how amazing it is versus the gui but it would be nice if somebody went ahead and made a visual tool
You know for just average everyday Joe’s
Windows 10
Anyways, enough of that before it clutters up this thread.
Been foolin’ around with this today. How do you deal with NAT in this configuration?
I set this up on pfSense and had all of my traffic tunneling through Linode. I ended up making a firewall rule/outbound NAT rules to force my server subnet to egress out of my regular WAN because I couldn’t get my portforwards to work. I had to write similar rules to make my wife’s PS4 work properly because she couldn’t play Crash CTR anymore lol…
So that depends on the host right? We have a second thread
Infrastructure Series -- Wireguard Site to Site Tunnel
But overall on pfSense it generates NAT rules by default from what I read… OPNsense does not…
By default OPNsense will not disable routes and let you make those decisions for yourself…
On linux you will find the same default. I summize there is potentially an issue with how you setup the PFsense firewall. Consult both threads. If you cant figure it out. Post your config (on either this thread or the other I linked) sans keys and see if someone can spot something
(Please noted in that thread IPv6 routing is not detailed)
iptables -D FORWARD -i %i -j ACCEPT; # In
iptables -D FORWARD -o %i -j ACCEPT; # Out
iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE; # NAT MASQ
#ip6tables -D FORWARD -i %i -j ACCEPT; # 6 in
#ip6tables -D FORWARD -o %i -j ACCEPT; # 6 out
#ip6tables -t nat -D POSTROUTING -o eth0 -j MASQUERADE # NAT 6 MASQ
(I havent quite figured out IP6 to IP6 wireguard yet. This will take exploration) but this should be a enough to get you started looking in the correct direction.