Donate $50 to the EFF and get a Security Key NFC
Hi all - apologies for bringing up this Necro thread BUT I just got a 5C FIPS key and was wondering if this HOWTO needs any updates since its 2022 intro?
I noticed this time around, at least on Mac, I’m missing Encryption key....: [none] and there’s no option to transfer the Enc key to the Yubikey.
However, at the time of creation and gpg --list-signatures shows SC, E, and SA keys. I tried deleting local secret keys and verified the yubikey is needed to secure Git commits. One difference I noticed
gpg> keytocard
Really move the primary key? (y/N) y
Please select where to store the key:
(1) Signature key
(3) Authentication key
Your selection? 1
gpg: WARNING: such a key has already been stored on the card!
ykman openpgp keys set-touch enc on
Enter Admin PIN:
Set touch policy of DEC key to on? [y/N]: y
Touch policy for slot DEC set.
It specifies a DEC key instead of an Enc key??
I do not have the FIPS keys
I cant test on mac either. Im in a linux household but ill tell you what. The post is wiki’d
Feel free to edit below the existing information with your findings. Dont erase information that exists unless its without a doubt in error
Thats FIPS terminology yes
Look into FIPS if it doesnt fit your needs its senseless to use. Its for federal information processing and encryption
One thing that seems a bit screwy on my end, and I need to check the gpg version:
gpg> addkey
Please select what kind of key you want:
(3) DSA (sign only)
(4) RSA (sign only)
(5) Elgamal (encrypt only)
(6) RSA (encrypt only)
(10) ECC (sign only)
(12) ECC (encrypt only)
(14) Existing key from card
Your selection?
This is the latest release too. All I’m doing is running gpg --expert --full-gen-key - but the options available do not match the wiki’d article above, hmm.
gpg (GnuPG) 2.4.5
libgcrypt 1.10.3
Copyright (C) 2024 g10 Code GmbH
I’m going to try create the keys on a linux system, then move them across.
EDIT: See my next post - I moved to using a sh script that also generates handy pre-revocation certs etc. This was cleaner than trying to do this on Mac.
I forgot that I had used a handy script in the past GitHub - bsodmike/Yubikey-GPG-SSH-FIDO2-MFA-ZeroTrust and just recreated a whole new key.
The only thing is this script creates a separate “C” key and “S” key, but it’s easy enough to use keytocard and move the keys one by one.
Thanks btw, this is working now UIF setting ......: Sign=on Decrypt=on Auth=on and all three keys are moved across.
BTW what do you prefer for encrypting data - VeraCrypt or LUKS? Not sure if I asked this before.
I’ve made some progress in updating this script with far better logging. I also like to add proper timestamps on any files generated so the tarball will look like - the following is just an example.
/tmp/tmp.0RRsJuDrMp
├── gpg.conf
├── gpg-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:18+0530-public.asc
├── gpg-DEF902068A4D62861DBBF9B4A748775BA503699F-mastersub-05072024-12:06:15+0530.key
├── gpg-DEF902068A4D62861DBBF9B4A748775BA503699F-sub-05072024-12:06:16+0530.key
├── gpg-gen-logs
│ └── gpg-gen.05072024.log
├── openpgp-revocs.d
│ └── DEF902068A4D62861DBBF9B4A748775BA503699F.rev
├── private-keys-v1.d
│ ├── 0CB18FE0DE4CCE943FBECA2B5DBCC1DE8DCA57D8.key
│ ├── 1C408544A2B4C5734DEFEF53A01C3A9D534BA1C7.key
│ ├── 60788215C44FB7C5C7C9B3AEC19F32E2B8ACCD14.key
│ └── ECC00FF16AB7AD41457B45D0D8B837A250EEBD46.key
├── pub1
│ ├── gpg-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:18+0530-public.asc
│ ├── revoke-compromised-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:14+0530.asc
│ ├── revoke-no-longer-used-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:14+0530.asc
│ ├── revoke-no-reason-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:13+0530.asc
│ └── revoke-superseded-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:14+0530.asc
├── pubring.kbx
├── pubring.kbx~
├── revoke-compromised-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:14+0530.asc
├── revoke-no-longer-used-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:14+0530.asc
├── revoke-no-reason-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:13+0530.asc
├── revoke-superseded-DEF902068A4D62861DBBF9B4A748775BA503699F-05072024-12:06:14+0530.asc
├── tofu.db
└── trustdb.gpg
5 directories, 23 files
I left the timestamp on the logs as “for the day” as internally it’ll have the actual timestamps as well. They look like ℹ [INFO] 05-Jul-2024 12:01:25 +0530 [gpg-gen][@builder0.debian12.foo.com] [376164] Exporting keys to disk...
These updates haven’t been made public yet, in due progress.
Hi mate, when time permits please see GitHub - bsodmike/Yubikey-GPG-SSH-FIDO2-MFA-ZeroTrust
- It’s using the latest hardened
gpg.conf - Proper timestamps added
- logging with the same and logs are copied to the backup tarball
- the script now supports
Usage: gpg_gen_yubi.sh name email <all extra emails> [output_path]- every email is added as an extrauidto the card.
You will still need to setup trust manually once you import the mastersub key.
Let me know if anyone has any issues or if there are any security concerns with the script - thanks!
This is excellent work on the fips side of stuff. Its not well documented by yubi. Ill take a look when I get a chance (on holiday)
Has the project been fully audited by external parties?
This could do with some sprucing up, just sharing a public version
Gosh, I’d be really worried trusting my keys to a 3rd party. I’m paranoid enough that I’d rather roll my own scripts and run these in a known safe sandbox - then encrypt (say VeraCrypt), then copy to an encrypted S3 bucket for example.
That was my second concern I wanted to get around to but I wanted to know if it was audited first
I actually love to be security audited. I learn so much
How is uploading encrypted secrets to AWS safer than keeping them on a an air gapped device?
Never roll your own stuff when dealing with cryptography. Go with tested.
Don’t know. It’s not obvious from their page. I do find the tamago unikernel thing really cool though.
Or at least get your stuff audited. It costs money bit creativity and new forms of encryption come from people testing new ideas.
If I cant find any. I may reach out and find out
Sorry, I mean’t custom utility scripts around pre-audited tools - Similar to the Git repo shared that just scripts around the gpg2 binary.
Regarding crypto - totally agree!!
I didn’t mean rolling an entirely bespoke solution - that’s definitely far worse as it needs to be battle tested across the industry, audited etc.
That said, I understand your point better now - thanks.
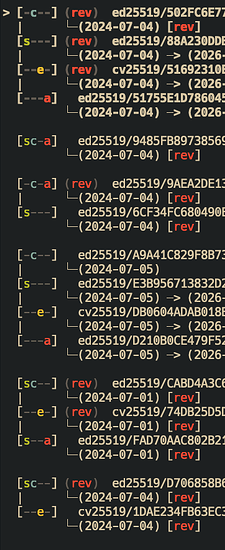
I’ve started modding GitHub - orhun/gpg-tui: Manage your GnuPG keys with ease! 🔐 and managed to get a quick improvement going. I want to be able to quickly filter and ignore revoked keys. The sub-key stuff has been implemented really nicely.
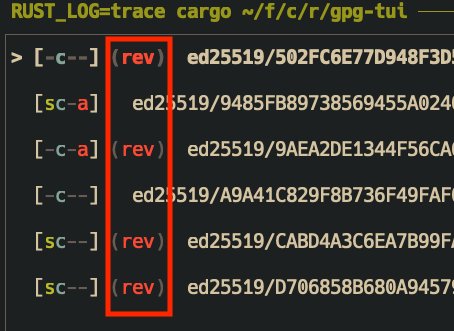
You can see how this plays out once expanded too. This crate wraps around gpgme-rs
FYI there hasn’t been much progress since March so I might work on this.
What’s the benefit of using GPG keys over SSH keys? Also, is there a way to use asynchronous cryptography for unlocking LUKS disks? Currently, I have configured a static password in the second slot of my Yubikey, but this could become problemmatic should I lose my laptop and my Yubikey together. That’s unlikely, imo, but it does mean that it is less secure than the password stored in my head for unlocking my LUKS disks.
P.S. I have a cold spare Fido2 key: Nitrokey Fido 2, but it doesn’t support ED25519 - which is why I replaced it with the Yubikey.