Hello there, Level1dwellers.
One day I port scanned all of the devices on my network.
And I’ve found that my ISP router has an SSH port opened, which made me curious. So I tried common combinations to brute-force it, but could not guess the credentials.
So I’ve looked online on how to get there, and I have found that there’s a higher user called ‘superadmin’
I called my ISP to get the creds, yet they played dump or didn’t get what I wanted.
So I looked into an exploit database, and I’ve found a patched exploit dates back to 2015 for an older firmware and an older model. (here)
I read it, and I’ve found that exploit showed that they did use an unencrypted base64 to store the passwords into the config file. (Extremely dump btw  )
)
The exploit also explains on how to extract the config file, cause you can’t extract it normally from the UI. You have to do a certain post request.
I tried to extract the config using the post request, but it did not work.
tho after trying my public IP instead it did work, and I got the config.
The password was encrypted tho with something a bit different than an unencrypted base64 (xD)
After further inspection I felt that it was just a salted base64.
So, I kept changing my regular admin password.
- make a new password > plain text password
- check the password change post request > shows an unencrypted base 64 password
- backup > shows an encrypted base64 password
After gathering those samples I was able to generate a simple model to reverse all the passwords from the config. Yep they were all encrypted with the same salt… 
- the firmware is actually not that old…
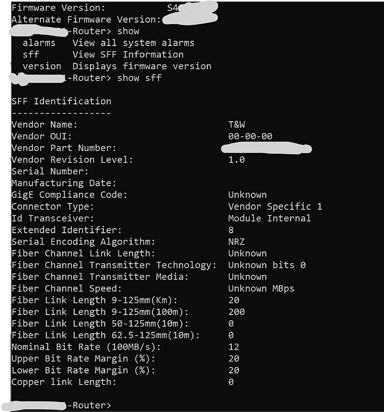
And wahaaaw I got the superadmin password. Yep as well as the SSH creds
Takeaway here
- ISPs are dump
- Somehow the hardware devs are incompetent.
- Much worse vulnerabilities could happen and a patches like this are insufficient!
- Trust not your ISP’s router.
- A useless ssh session

* * To be fair I was able to figure out on how to automate too many things, but I use pFsense already…
-pakxo.