Hi,
I was wondering would anyone be able to help me get a better understanding of how LVM and LUKS work together on Linux storage devices?
I had another thread where I was trying to understand the best way to re-partition a data drive I had but while looking into that issue I found that my SSD is not being utilised as well as it should and I would like to address that first. I did add to that thread but my post was too wordy and probably didn’t make much sense.
So I thought I’d see if I could be a bit more concise here.
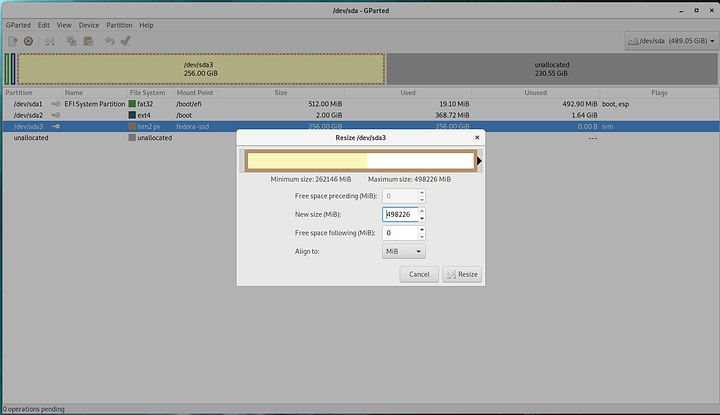
I have an SSD with the following partitions:
NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT
sda 8:0 0 489.1G 0 disk
├─sda1 8:1 0 512M 0 part /boot/efi
├─sda2 8:2 0 2G 0 part /boot
└─sda3 8:3 0 256G 0 part
└─fedora--ssd-root 253:0 0 256G 0 lvm
└─luks-fa9f909c-6a08-4554-b354-074aa04a80ee 253:3 0 256G 0 crypt /
There is a single LVM volume group for the SSD called fedora-ssd
--- Volume group ---
VG Name fedora-ssd
System ID
Format lvm2
Metadata Areas 1
Metadata Sequence No 2
VG Access read/write
VG Status resizable
MAX LV 0
Cur LV 1
Open LV 1
Max PV 0
Cur PV 1
Act PV 1
VG Size 256.00 GiB
PE Size 4.00 MiB
Total PE 65536
Alloc PE / Size 65536 / 256.00 GiB
Free PE / Size 0 / 0
VG UUID iLJ7iR-npsd-D4OY-cVWs-Wvoy-KIdG-RYYH39
From what I understand, the “fedora-ssd” volume group is backed by only the /dev/sda3 partition/physical volume and does not really represent the entire SSD (/dev/sda1 and /dev/sda2 being outside of LVM because they are needed during boot)
--- Physical volume ---
PV Name /dev/sda3
VG Name fedora-ssd
PV Size 256.00 GiB / not usable 2.00 MiB
Allocatable yes (but full)
PE Size 4.00 MiB
Total PE 65536
Free PE 0
Allocated PE 65536
PV UUID 8OWONx-Y8nW-1Y3A-fqyw-eDmM-UGzz-zlLaJn
Is this correct so far?
I would like to move my /home partition to my SSD. There’s about 248GB of space un-allocated on the SSD but the existing root partition is far to big so I would also like to reclaim some of that space.
So my second question is, what is the best way to do this?
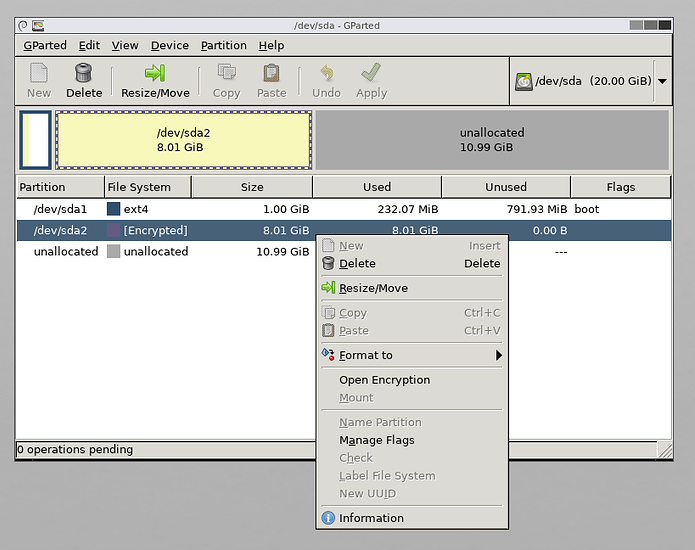
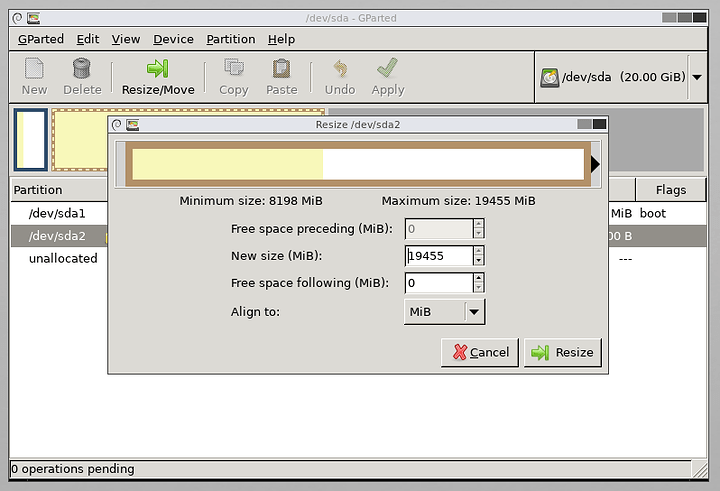
My first thoughts were to resize /dev/sda3 to between 60-80GB (I’m currently only using 11GB) then create /dev/sda4 with the remaining space on the SSD for /home.
But the more I think about it the more I realise this seems like how things would have been done before LVM. And I would also like the new /home to be encrypted so would probably have to create a new LUKS volume for the new /dev/sda4
Instead, If I were to expand /dev/sda3to fill the remaining un-allocated space on the SSD (giving it approx 500GB), would this space then be available to the fedora-ssd volume group (and more importantly still part of the existing LUKS volume)?
Is so, can I then shrink the fedora-ssd-root logical volume to 60GB with lvreduce and create a new fedora-ssd-home logical volume that takes the remaining space in the fedora-ssd volume group.
Again sorry for the length of the post, I tried to keep it as sort as I could, but does the second approach sound reasonable or am I still not understanding LVM correctly?
Any advice or clarification would be appreciated.
Thanks




 )
)

