so, most (if not all) of the assertions in that blog post are demonstrably false. examples:
The CIA didn't defeat Signal/WhattsApp encryption.
The wikileaks PR references bypassing of the encryption via mobile rootkits and control software, of which there are quite a few in the leak. They never state that the apps themselves have been compromised.
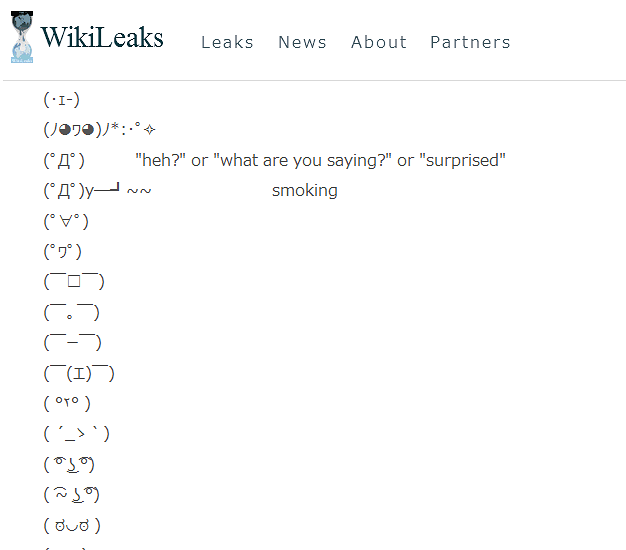
See:
These techniques permit the CIA to bypass the encryption of WhatsApp, Signal, Telegram, Wiebo, Confide and Cloackman by hacking the "smart" phones that they run on and collecting audio and message traffic before encryption is applied.
The CIA isn't hoarding 0days.
There are quite a few PSP bypasses in the release. The CIA did not disclose these vulnerabilities. at best this is arguing semantics. At worst, a bold-faced lie.
The CIA didn't remotely hack a TV.
Not once does the Release imply that the code is deployed remotely
There's no overlap or turf war with the NSA
The release never states this. It does mention that the CIA has been building parallel infrastructure to the NSA, and has recently been expanding its reach and budget, which is veritably true. It then goes on to cite several instances of NSA/CIA COOPERATION
The CIA isn't more advanced than the NSA.
The CIA isn't spying on us.
Again, not once does the press release mention any spying on US citizens, nor does it intone that the CIA is more advanced than the NSA.
The CIA is not cutting edge.
I'm having to repeat myself ad-nausem here. The author of this blog post is pulling attribution from thin air
The rest of their assertions are either opinions or speaking with authority about things they have no expertise in, a la
The VEP process is nonsense.
There's no false flags.
or
This hurts the CIA a lot.
in which our "security expert" admits that more competent people have told him this assumption is false.
I'd recommend you read the source material before posting things like this. The author of this blog post either has very poor reading comprehension or has a specific message to push. He's batting .00 on the facts.