Perfect timing, I wanted to get into Linux and VM’s, I guess this is just the impetus.
The Stilt is responding (finally):
PCI you say?
Because I have a bunch of bluescreen dumbs with PCI Id something something error
Just testing it right now.
Also god damn AutoIt code is awful. The way it does it’s compilation is even crazier. Just embeds the whole autoit3 exe in the binary with the compiled autoit script appended to itself in the binary.
So you can co-opt such an exe to extend its abilities any way you want.
Time to deobfuscate those ‘secret register’ values. 
God I’m so going to rewrite this thing in some sane code. AutoIT Scripting is possibly more disgusting than VB6 to look at.
Totally needs more globals 
I was wondering this earlier and original seemed to be ok, I felt uncomfortable with that 1.01 and kept on using that original
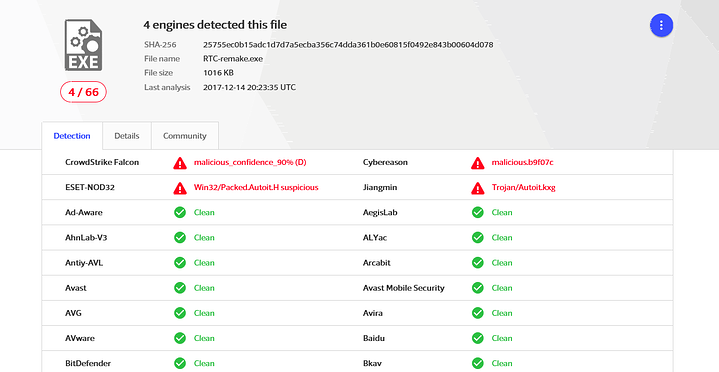
I guess I’m a better obfuscator?  Only 4 detections on VT.
Only 4 detections on VT.
But that doesn’t really mean much.
It’s odd though how Cyber reason now detects this but doesn’t detect the original RTC. Maybe I should ask Amit?
I kept on using that original one till last week, shame it got formatted so I cant give it to compare whats going on

You have that 1.0?
I guess yes
Ahh shucks. Now I’m back at the point where I need a copy of exe2aut to hack with. That old program has got rather hard to find and fell out of my tools collection at some point.
Possibly found a workaround with a different tool.
Aww Yissss. I’ve decompiled the obfuscated original AutoIt script with all variables.
Here is the code, it may still be a little filthy.
This is the code posted by the stilt.
Obviously with the obfuscation a lot of chaos was introduced.
So I have included the obfuscated version of the sanitzied code that the stilt posted.
As you can probably tell it’s disgusting to read.
I’m going to sleep now.
But yes this includes all the ‘secret registers’.
I’ll patch the released code with this extracted code tomorrow. Tired as hell now.
And before I forget!
No Malware in the AutoIt Script. Just awful awful code 
My sincere apologies to @thestilt and everyone that’s formatted their Windows install.
Be vigilant with what code you run. Only trust a binary you’ve backdoored yourself 
Long live Open Source / GPL !
Well that’s damn good news at least!
Thanks so much for that.
Thanks that is a relief. I built pcs for some pretty sophisticated and nice people
update: i was looking over my customers pc and I really was not in the mood to have to reinstall windows and back everything up, but i had to do the due diligence.
anyhow as i was struggling to get the pc to post with 64gigs of ram, I had turned on bootlogging using the bcdedit /set bootlog yes command which produced nothing unusual there. Or so I thought.
Today I looked at the C:\windows\ntblog.txt and I found this :
BOOTLOG_NOT_LOADED \SystemRoot\system32\drivers\WdFilter.sys
BOOTLOG_LOADED \SystemRoot\system32\Drivers\WdNisDrv.sys
BOOTLOG_LOADED ??\C:\Program Files (x86)\Samsung\Samsung Magician\magdrvamd64.sys
BOOTLOG_LOADED \SystemRoot\System32\drivers\tunnel.sys
BOOTLOG_LOADED \SystemRoot\System32\drivers\WSDPrint.sys
BOOTLOG_LOADED
BOOTLOG_LOADED ??\C:\Users\geoffh\Downloads\RTC_1.01\WinRing0x64.sys
I thought this is strange as I have never seen a boot item with no name loaded, and also that RTC program sys file should not be loaded during boot as I have never installed it as a startup item or service. After this one appearance, it is never appearing in the bootlog. Can anyone else verify this? Strange but kind of exciting and titilating
That’s the Kernel Mode Driver used to do the low level hardware (PCI) access. I have no idea where it comes from, but a lot of places such as CorsairLink, OpenHardware monitor etc used to use it. It can be loaded by a bunch of applications actually.
SO unless you have another program loading it for hardware monitoring. It shouldn’t be bound at boot. Only while the actual RTC is running.
That said I haven’t gone over the WinRing0 code yet. It’s a separate thirdparty dll called by the AutoIt scrpit to perform the actual PCI Bus Config R/W.
There is a copy of some ?archived? source code of it available that might be recompilable/reusable.
Hey !
Not sure it seems to be the one included by the stilt app. This is nuts. Also in all my years, I never had a BOOTLOG_LOADED blank entry. Crazy
I was going to ask if you could share that original one because I cant find it, but that 1.01 unfuck patch sounds better 
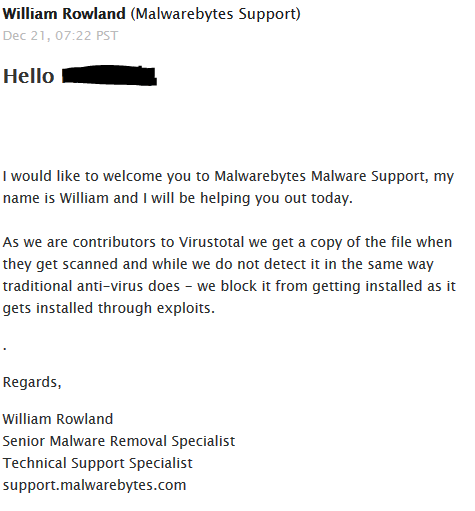
Contacted malwarebytes about it:
a 1.02 was released, re-coded in C#
that is crazy. Well i am glad I nuked those boxes. All those boxes…pretty shocking either way.