Hello good sir, did you get a chance to benchmark the 3930 pre and post patch? I have two here and wondering if I should patch them or not… I will eventually have too, just want to make sure i’m not killing the rest of the power I have 
Thanks!
Please see below. but was already posted above.
not huge Difference
Woops must have missed it while searching. Thank you sir!
Yes if only I had a ryzen laptop. I hope intel gets its shit together. I havent looked into the details of the security flaw but the performance impact alone I feel might actually be noticeable. TO my knowledge however is that the attacks are simply informational aka read only attacks…
The real question is with such a huge bug affecting so much why are we just now discovering it?
I guess it brings to light the advantages of opening the architecture up a bit. I think once I watched a video discussion between lunduke and of course the rather more infamous RMS about how we continue to build and build architecture ontop of previous architecture whos bugs havent fully been discovered yet and that something like this might eventually occur. Its kind of funny to see that this all came into alignment.
I have already looked into patching my systems as of January 3rd
@wendell Is there an up to date, compiled list of links or something I can give to my boss at work. I work in IT and he sent company wide email containing a Yahoo Money article Friday or something and I was like, "dude Ive been tracking this all week. " I want to hook him up with the good information not that crap he gets thats filtered by the MSM.
Uhm, have you seen the first post of this thread?
People are paying you for this as part of your job. Do the work and come up with the research and a report if needed.
Well, I don’t care.
And speaking of …
Maybe don’t ask for help by starting with the words ‘I need’?
you are correct. I will adjust my request post accordingly.
Here is a list of the links I have so far for reference:
Summary
https://wccftech.com/intel-kernel-memory-leak-bug-speculative-execution-performance-hit/
https://newcmi.com/security-bulletin/intel-security-bug-meltdown-spectre/
https://thehackernews.com/2017/11/intel-chipset-flaws.html
https://thehackernews.com/2018/01/meltdown-spectre-patches.html
https://thehackernews.com/2018/01/meltdown-spectre-vulnerability.html
https://thehackernews.com/2018/01/intel-kernel-vulnerability.html
https://www.fsf.org/blogs/community/active-management-technology
https://arstechnica.com/information-technology/2017/11/intel-warns-of-widespread-vulnerability-in-pc-server-device-firmware/
https://www.bankinfosecurity.com/intels-amt-flaw-worse-than-feared-a-9901
https://meltdownattack.com/
http://www.zdnet.com/article/how-linux-is-dealing-with-meltdown-and-spectre/
http://www.zdnet.com/article/security-flaws-affect-every-intel-chip-since-1995-arm-processors-vulnerable/
https://www.extremetech.com/computing/248919-major-intel-security-flaw-serious-first-thought
https://www.npr.org/sections/thetwo-way/2018/01/04/575573411/intel-acknowledges-chip-level-security-vulnerability-in-processors
https://www.wired.com/story/meltdown-and-spectre-vulnerability-fix/
https://seekingalpha.com/article/4135558-intel-security-risk-much-worse-management-commentary-indicates
https://www.tweaktown.com/news/58520/intel-cpu-engineer-leaves-20-years/index.html
https://www.fool.com/investing/2017/12/19/intels-ceo-just-sold-a-lot-of-stock.aspx
https://googleprojectzero.blogspot.com/2018/01/reading-privileged-memory-with-side.html
Yes, is that not normal?
A 2u rx2600 providing thermal mass in my basement. Was just starting to mentally part with it…
Yeah, don’t hide it behind a spoiler, it accidentally clicks the link for those of us what want to open the links in a private window cause cookies.
I see a few links related to the AMT problems in that list. Don’t confuse these with spectre and meltdown.
The embargo is still up until tomorrow. I expect there will be more info then.
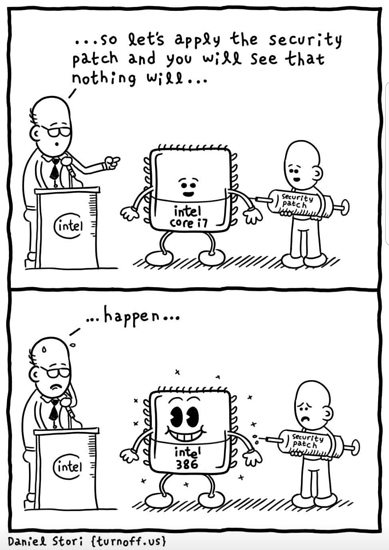
Meltdown patch in action gallery:
Five graphs with source links. All I’ve seen so far. All pretty bad.
Graphs collected by /u/ceremony64.
I included those to show how far back these problems have been. Most were not even aware of the AMT issues and we are trained to configure AMT on boards. I thought they should know.
Usually the spoiler does what the Details this does but it is now behind the Details.
The sad reality of meltdown.
And why it makes most businesses no less secure than before 
Login without a password as usual 
| CVE | Group | GPZ number | GPZ naming |
|---|---|---|---|
| CVE-2017-5715 | Spectre | variant 2 | branch target injection |
| CVE-2017-5753 | Spectre | variant 1 | bounds check bypass |
| CVE-2017-5754 | Meltdown | variant 3 | rogue data cache load |
Exploit homepages are spectreattack.com and meltdownattack.com, although both are the same.
Summaries so far
- @Noenken has a summary in his OP of this thread.
- I @torpcoms have a summary post in this thread that I still edit.
- @Freaksmacker was impressed by the summary from Carnegie Mellon’s SEI CERT (not US-CERT).
- Google has a quick summary, and a post on Project Zero’s blog.
- @catsay recommended Hector Martin’s summary/repo of helpful links on github.
- Bruce Schneier also has a link repository
- @noenken recommended the Raspberry Pi Blog’s post, which is pretty much Speculative Execution for Dummies. Not a summary, but really useful for explaining to others or yourself.
Here are some official pages from US Gov CERT or UK Gov CERT if that is more your thing. CERT-EU is just a glorified RSS/Atom reader, and doesn’t have a page.
@catsay also started a thread for trying to list CPUs that are not vulnerable at all, and I am trying to figure out what the situation is for POWER/PowerPC here.