Perfect! I’ll try it!
Check your work policies but introducing malicious software here would be likely be gross misconduct and immediate dismissal so stick a nice sign up stating that 
That’s nothing, not too long ago I went to a site where their entire network was mostly populated by 10mbps flat switches with no VLAN capability, it was just one giant collision domain. There wasn’t the money to upgrade and most of the cabling was 20 years old ! Management was clueless and the one guy in charge was just a few years away from retirement…
Pah, 10mbps flat switches! You don’t know you were born! I was working at one site where all they had was token ring (No, not a Tolkien Ring!) and for Christmas they thought they were lucky if the company director gave them a sixpence…
Do you have access to group policy? Either local or domain is fine. If local:
start and search for gpedit.exe
Computer Configuration (or user) -> Administrative Templates -> System -> Removable Storage Access
Disable the ones you want to disable by enabling the policy.
gpedit.msc
Jesus these forums… people nit pick on the smallest things.
I know it’s .msc else I wouldn’t recommend the group policy stuff. Windows is smart enough to pull it up now with .exe, no reason to worry about msc which may make someone go “wooo I don’t know what msc is I’m not touching that.”
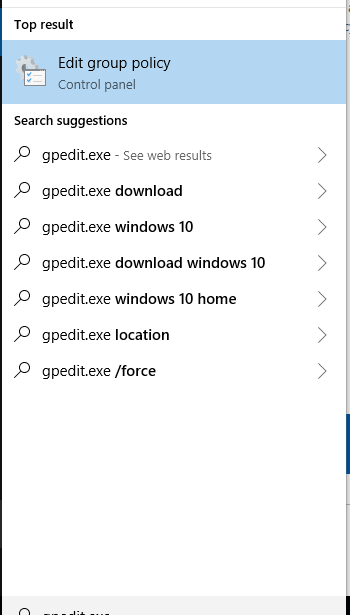
For some reason the bottom part of the snippet got cut.
Today I learned win10 will run a Msc if I mistyped. I dislike/ hate on windows a little less now…
Not nitpicking, just didn’t know it would actually find and execute the .msc in the search. Because when you try to run it as .exe via Win+R it just throws an error in your face.
The run prompt is looking for specifics, the search bar is looking for keywords.
If you’re using Windows and still looking at solutions, and you don’t want to go so far as disabling usb devices or something, I’d say sandboxing is something worth exploring. Others have already brought it up by suggesting virtual machines + snapshots, but using a sandboxing application should give you the same benefits without all the overhead that comes from running a full VM.
I haven’t done much testing on sandbox applications myself, but there’s lots of info out there from people who have tested it. The only thing I’ve tested was wannacry on an un-updated version of Comodo and Sandboxie and both stopped it from doing any damage to my PC.
Comodo has an auto-sandbox feature that seems pretty on point. In the way a virus program has a blacklist (allow all files unless they match the malware in its database), Comodo’s sandbox uses the opposite approach and trusts nothing unless it has a verifiable signature from a trusted vendor. In this sense it should work on unknown threats as well (and seems to handle that well in testing). So it doesn’t directly address the USB situation, but if that USB has any kind of auto-executing malware on it, Comodo would sandbox it.
Another solution I use is Sandboxie. I think this feature may require the paid version, but I’ve set up a sandbox that forces every file/executable/etc in a certain drive to run in the sandbox. There’s tools out there you can use to force usb storage devices to mount at the same letter each time, like this, and then just have your sandbox set up to intercept anything coming from that drive letter. In my experience, this has worked quite well, even with scripts set to auto-run.
Just keep in mind that with this setup, if you plug in your own USB drive, open up a word document on it, edit the document and save it, that edited document will be saved in your sandbox, not on your (unsandboxed) PC or on the USB drive. So it’ll take a couple of extra mouse clips to save the edited version onto your PC (outside of the sandbox) or onto the USB drive.
if it’s mostly just work related:
-install ubuntu
-install libreoffice
-install master pdf editor.
this will allow basic auto mount/unmount of usb sticks, file transfers, excel/word compatibility, and pdf compatibility on the machine, with no viruses.
if you need to print, also install cups
if you need network shares, install samba client
if you absolutely need windows for something, install virtualbox and create a small windows vm. Mine is set for 1 processor, 4gb ram, 50gb hard disk space. For example I need this for running stamps.com software, as the rest of the office uses this and i have no control over that.
I’ve been using this setup at work on my arch machine for the past 3 years. I work as an IT admin for a small law firm, and we quite often get regular spam virus phishing pdf emails
do NOT install wine if going this route. windows viruses will happily run under wine.
@Yockanookany sorry man, I appreciate the post, but thought Microsoft remapped msc and exe commands… wasn’t nit picking or meaning any bad things, just genuinely was mistaken.
Lots of major corporations just ban usb sticks by policy (talking about organizational, not windows/group), and use some kind of shared/cloud storage instead. Make sure you have management buy in, usually the policies are made to be bypassable with management approval that can be given via email. Knowing violation of policies is usually a fireable offense.
Historically, getting employees to plug in USB sticks has been way too easy, you should generally not run into them in a well managed org.
bingo, also hence the virtualbox vm
literally no reason to install wine on a work machine anyway
Yeah I came off a bit strong there, sorry. It’s just gotten to the point that these forums has become a cesspool of people trying to see who’s the smartest by finding the smallest things to nit pick about to show how much knowledge they have in such niche things. I’ve grown weary of it.
Anytime I tell a user to search anything I just tell them to put .exe. behind it… if I tell them to put anything at all. Makes life easier.
At work we use usb locks that physicaly block the usb port and are damm hard to get out of the port without the required key.
https://www.lindy.co.uk/usb-firewire-c4/usb-port-blocker-pack-of-4-colour-code-blue-p2324
I also disable the all mass storage devices in group policy.
You can specify a specific id to allow also (for your own stick)
And i also disable of physicaly disconnect any chassis ports if it is possible.
We do this on our thin clients.
Is there no way to lock the room? Server rooms should really have access control.
Look into Abloy for a lock.
This is a workstation machine as I understand, not the server.